1. About this document
This document provides the step-by-step procedure to configure the Tenable Security Center in SAFE.
2. Introduction
SAFE integrates with Tenable Security Center and allows you to discover and import assets from Tenable Security Center along with the respective vulnerability assessment results in SAFE.
Here are the key highlights of this integration:
Import Assets and Vulnerability Assessment Results: With this integration, you can now discover and import assets from Tenable Security Center along with the respective vulnerability assessment results for a comprehensive view of your assets' security posture.
Automated and On-Demand Sync: You can set a pre-configured time interval for automatic synchronization of assessment results for assets. Also, it allows you to initiate on-demand pulling of assessment results for assets as needed.
On-Premise Connector: Tenable Security Center is an on-premises deployed solution, and now, SAFE supports seamless communication with it. Configure an on-premise connector in your environment using Docker technology that ensures a secure and efficient data transfer between Tenable Security Center and SAFE.
3. Prerequisites
3.1. Functional Prerequisites
To proceed, make sure the following prerequisites are met:
Host Machine with Docker: You must have a host machine with Docker already installed. This will be used to download, install, and configure an on-premise Docker-based component that facilitates communication with SAFE.
Note
You can refer to the official Docker documentation for installation steps specific to your server’s operating system. Example links for commonly used operating systems are provided below:
Tenable Security Center credentials for accessing their APIs (Refer to Generate keys)
Access Key
Secret Key
Note
The user for SAFE must have the Vulnerability Analyst role. This is because this role is required to be able to extract the required data from the APIs. A Security Manager role does not have permission to access the APIs and will result in the sync failing.
SAFE API Credentials: Refer to Accessing SAFE APIs to create SAFE API credentials.
Network Access: Your host machine should have network access to the following resources:
SAFE Instance: refer to SAFE’s Outgoing IP Addresses
Tenable Security Center Instance
Encryption Key: SAFE's on-premise connector for Tenable Security Center employs offline encryption to secure both Tenable Security Center and SAFE API credentials stored on the local machine. To enable this encryption, an exact 32-character encryption key is required. This key must be provided each time the container needs to be initiated, updated, or restarted. You can generate a 32-byte encryption key using online tools such as RANDOM.ORG's String Generator.
3.2. Host Prerequisites
To host the connector successfully, your server must meet the following prerequisites.
Docker Engine: Ensure that Docker Engine is installed and operational on the server where you intend to deploy the connector.
For optimal performance and compatibility, we recommend the following server specifications:
CPU: At least 2 virtual CPUs (vCPUs).
RAM: A minimum of 8 Gigabytes (GB) of RAM.
Storage: Allocate at least 100 Gigabytes (GB) of disk storage.
4. Configure Tenable Security Center with SAFE
4.1 SAFE Setup
Login to SAFE as Admin.
Navigate to Integrations, on the left navigation.

Click the Tenable Security Center card.
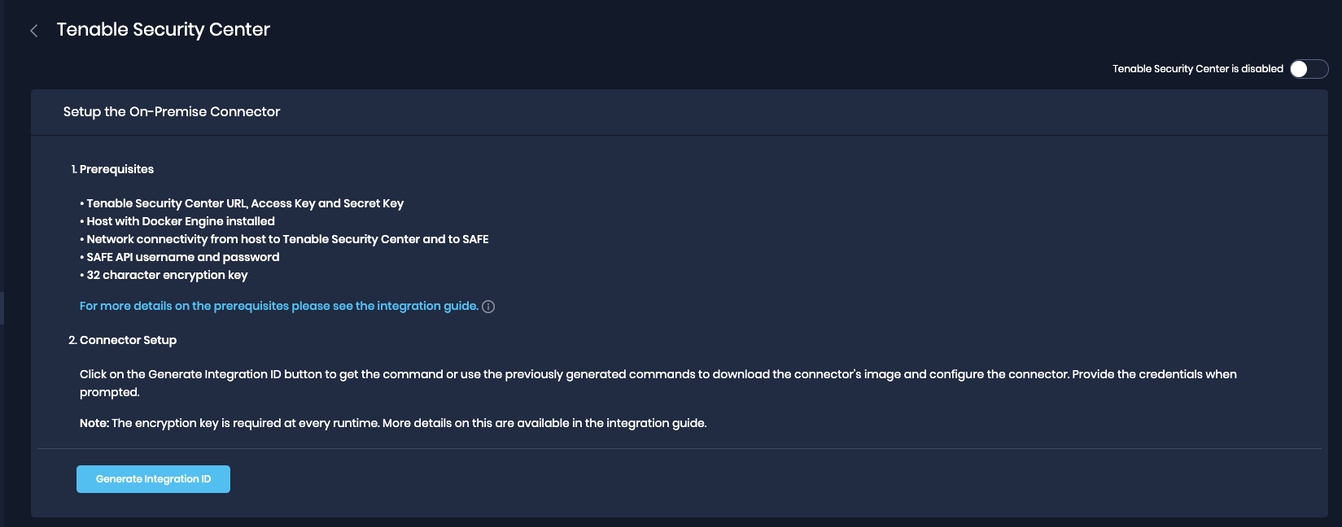
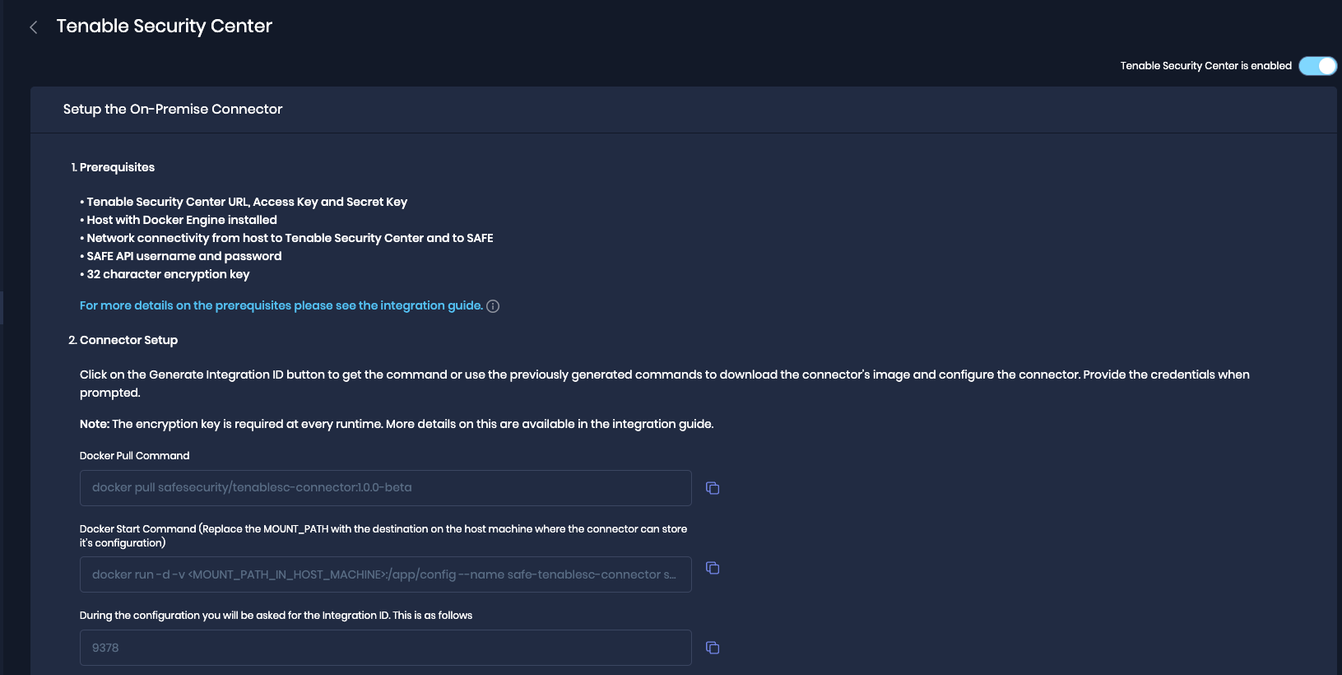
Click on Generate Integration ID. The system displays the Docker Pull command, Docker Start Command, and Integration ID. The generated commands need to be configured on the on-premise connector, as covered in the next section.
4.2. On-Prem connector setup
Run the Docker Pull Command on the terminal.
Below is an example command, use the command generated above in step 4.1.4.docker pull safesecurity/tenablesc-connector:1.0.0Run the Docker Start Command and replace '<MOUNT_PATH_IN_HOST_MACHINE>' with the actual value.
Below is an example command, use the command generated above in step 4.1.4.docker run -d -v <MOUNT_PATH_IN_HOST_MACHINE>:/app/config --name safe-tenablesc-connector safesecurity/tenablesc-connector:1.0.0 && docker exec -it safe-tenablesc-connector bash initialise.shFill in the required details as per the prompt shown on the terminal.
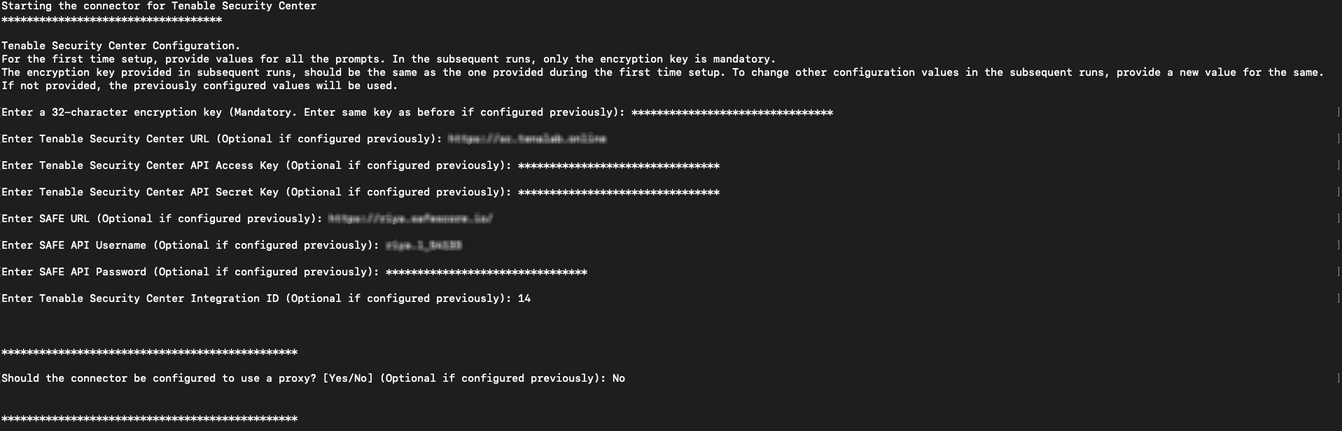
Note
For the first-time setup, provide values for all prompts. In the subsequent runs, only the encryption key is mandatory.
The encryption key provided in subsequent runs should be the same as the one provided during the first time setup. To change other configuration values in the subsequent runs, provide a new value for the same.
4.3. Proxy Setup (Optional)
Follow the below steps to set up the proxy:
On the prompt Do you want to configure a proxy? (Yes/No): If Yes, fill in all the required fields, which are present below.
Leave all fields empty if the proxy was already configured once and you want to keep it the same.
Enter proxy IP (Optional if configured previously): <IP>
Enter proxy port (Optional if configured previously): <PORT>
Enter proxy username (Optional if configured previously): <PROXY_USERNAME> If configured on Proxy
Enter proxy password (Optional if configured previously): <PROXY_PASSWORD> If configured on Proxy
Enter comma-separated list of no proxy IP/DNS (leave empty if none): <IP>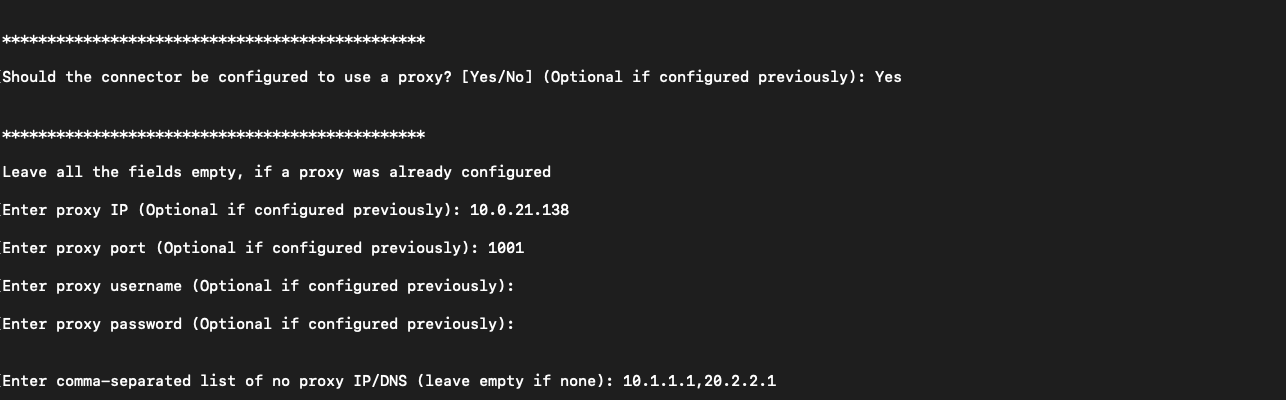
4.3. Save Configuration
Navigate to the Integrations, on the left navigation, and click the TenableSecurityCenter card.
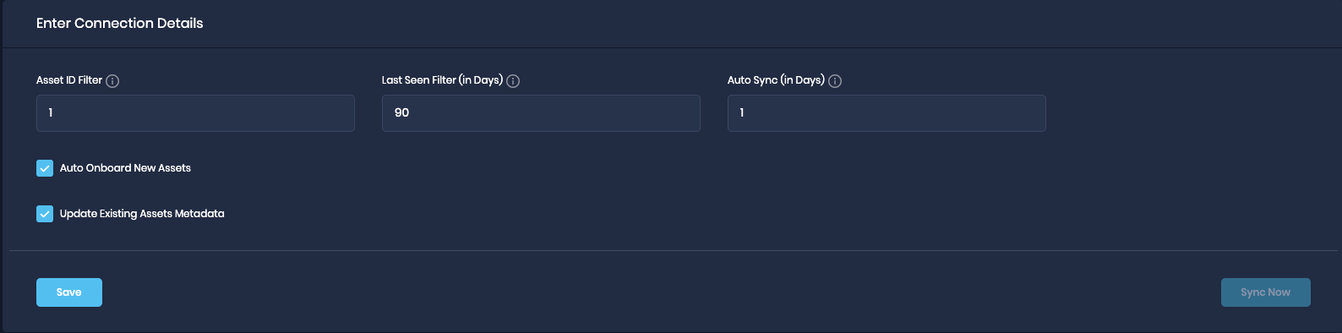
Under the connection details, enter the AssetID Filter. Asset ID value can be comma separated, e.g., 1,2.
SAFE allows the user to filter the data being fetched from the Tenable Security Center based on the Asset IDs. If not provided, all asset data to which the user has access will be pulled into SAFE.
Fill in the Last Seen Filter (in Days). The Last Seen filter will configure the connector to fetch the vulnerabilities found in past <N> days. The default value is set to 90 Days.
Enter the Auto-sync frequency in the number of days.
Click the Save button.
Once the configuration is saved, click the Sync Now button to trigger the on-demand sync outside of the scheduled auto-sync.
5. View Results
To view the Onboarded assets
Go to Technology, on the left navigation.
Click on the funnel to filter by onboarding source as Tenable Security Center.
.png)
All the relevant assets are listed.

6. FAQs
6.1. What to do if the Encryption key is lost?
Follow the steps below if you lost the Encryption Key:
Remove the previously mounted config path directory on the host machine.
Reconfigure the On-Premise connector as mentioned above.
6.2. How to upgrade the connector when a newer version is available from SAFE’s end?
Follow the steps below to upgrade the connector to a newer version:
Stop the currently running On-Premise Connector using the following command:
docker rm -f safe-tenablesc-connectorCopy the Docker pull command (which would have been updated with a newer version).
After pulling the latest image for the Tenable Security Center On-Premise Connector, go ahead with the starting command (i.e., the second command on the Integrations Page of Tenable Security Center).
Keep the config path as earlier configured; there is no need to change that.Enter the Encryption Key when prompted.
The user is not required to fill in any other details again (if configured already).
6.3. How to use private SSL certificates with an on-prem connector? (with Deep Packet Inspection-ing Firewalls)
To utilize private certificates with the on-prem connector, customers must ensure that these certificates are accessible within a designated directory on the server or machine where the connector is being configured, referred to as "<CERTIFICATES_DIRECTORY>."
Additionally, you will need to specify the path of the certificate required for accessing the SAFE server from within the container. For example, if the certificate is named "ca-certificates.crt," the path to this certificate file will be "/etc/ssl/certs/ca-certificates.crt," denoted as "<CA_CERTIFICATE_FILE_PATH>."
To enable the connector to function with these certificates, you must modify the Docker Start command (2nd command on the Tenable Security Center configuration page).
Original Command:
docker run -d -v <MOUNT_PATH_IN_HOST_MACHINE>:/app/config --name safe-tenablesc-connector safesecurity/tenablesc-connector:1.0.1-beta && docker exec -it safe-tenablesc-connector bash initialise.sh
Modify the above command to include support for private certificates, resulting in the updated command:
Updated Command with Support for Private Certificates:
docker run -d -v <MOUNT_PATH_IN_HOST_MACHINE>:/app/config -v <CERTIFICATES_DIRECTORY>:/usr/local/share/ca-certificates -e NODE_EXTRA_CA_CERTS=<CA_CERTIFICATE_FILE_PATH> --name safe-tenablesc-connector safesecurity/tenablesc-connector:1.0.1-beta && docker exec -it safe-tenablesc-connector bash initialise.sh