About this document
This document provides the step-by-step procedure to integrate SAFE with Qualys Security Configuration Assessment (SCA) and Policy Compliance (PC).
Introduction
SAFE integrates with Qualys Security Configuration Assessment (SCA) and Policy Compliance (PC) to fetch the configuration assessment results based on CIS benchmarks into SAFE. Once configured, this integration onboards the Qualys SCA and PC assets in SAFE and automatically adds assets to Default groups based on the Operating System (OS) information from Qualys.
You can configure Qualys SCA and PC in SAFE from the Qualys SCA card available in the Integrations on the left navigation.
Supported Asset Type
Qualys SCA and PC integration supports the configuration assessment for the following asset types:
RHEL 7.x
RHEL 8.X
CentOS 7.x
CentOS 8.x
Ubuntu 22.x
Ubuntu 20.x
Suse Linux 12.x
Suse Linux 15.x
Windows 8.1
Windows 10
Windows 11
Windows Server 2012 R2
Windows Server 2016
Windows Server 2019
Windows Server 2022
Notes
If SAFE does not find the mapping for an asset, the asset will be added to the Others Default Group. However, you can move the asset manually to the best-suited Group.
You can check the mapping using API “GET <SAFE_URL>/api/v3/settings/os-to-safe-asset-type-mapping”.
To add a custom OS to Safe Asset Type mapping, use API “POST <SAFE_URL>/api/v3/settings”
By default, the asset-matching criteria used for Qualys SCA is ["fqdn", "assetName", "ipAddress"]
Prerequisites
To configure Qualys, you need the following details:
Qualys API URL - The URL should start with qualysapi, and not qualysguard.
Qualys API Credentials
Verifying that the SAFE Instance’s IP address is whitelisted in the user’s Qualys Instance.
Create a user in Qualys with API access
To connect Qualys SCA and PC with SAFE, you can use an existing user’s username and password, which has access to the Qualys API, or create a new user. The minimum access required for the user is Reader level, and the user should have both GUI and API access to set up the integration properly.
Note
You need Admin access to create a new user in Qualys.
If you have configured Qualys to use SSO for all users, you will need to disable SSO for the API user. To do so follow this Qualys documentation, Go to Users > Users and edit the user's account. You'll see the SAML SSO option in the Security section.
Create a new user in Qualys
Log in to your Qualys instance.
Scroll down and select Administration from the top-left dropdown.
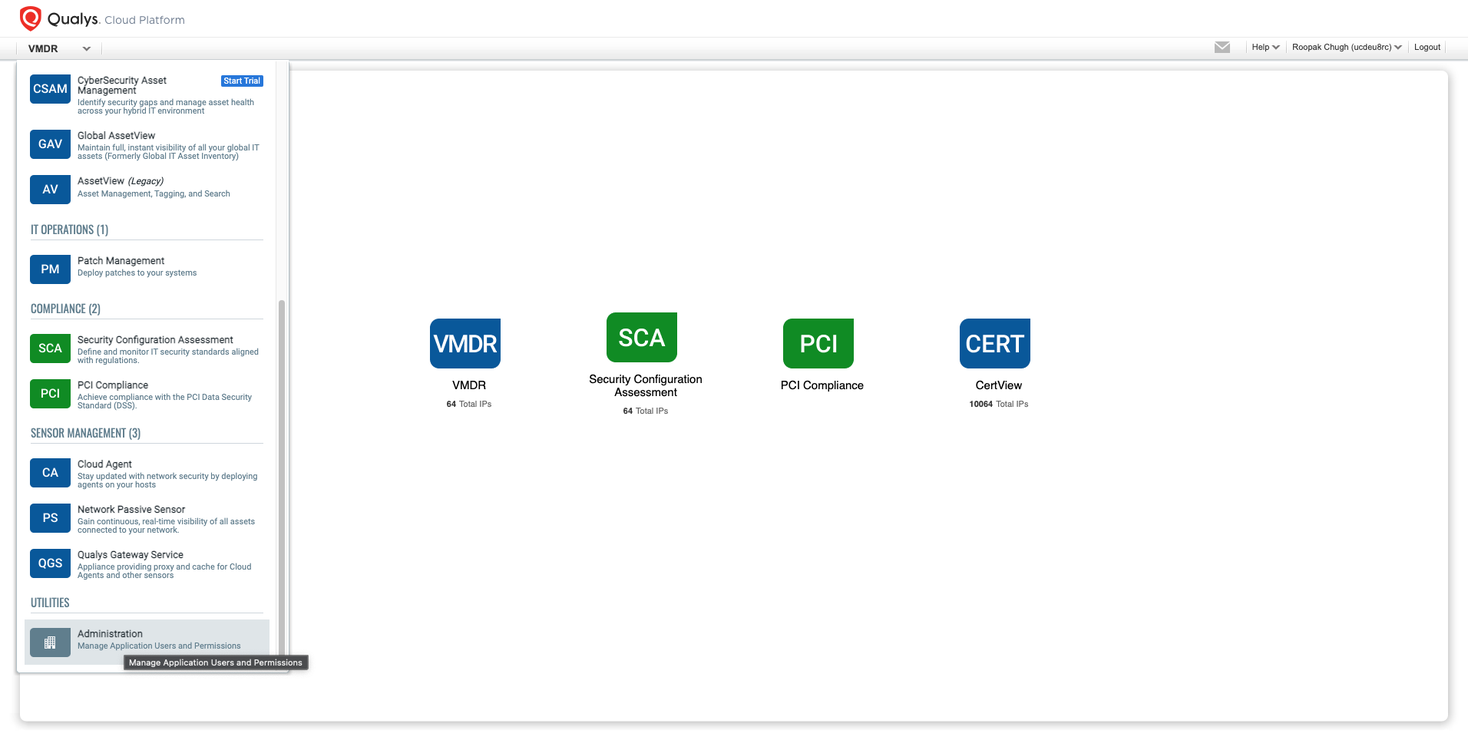
Click the Create User button on the Administration page and select CreateReaderUser.
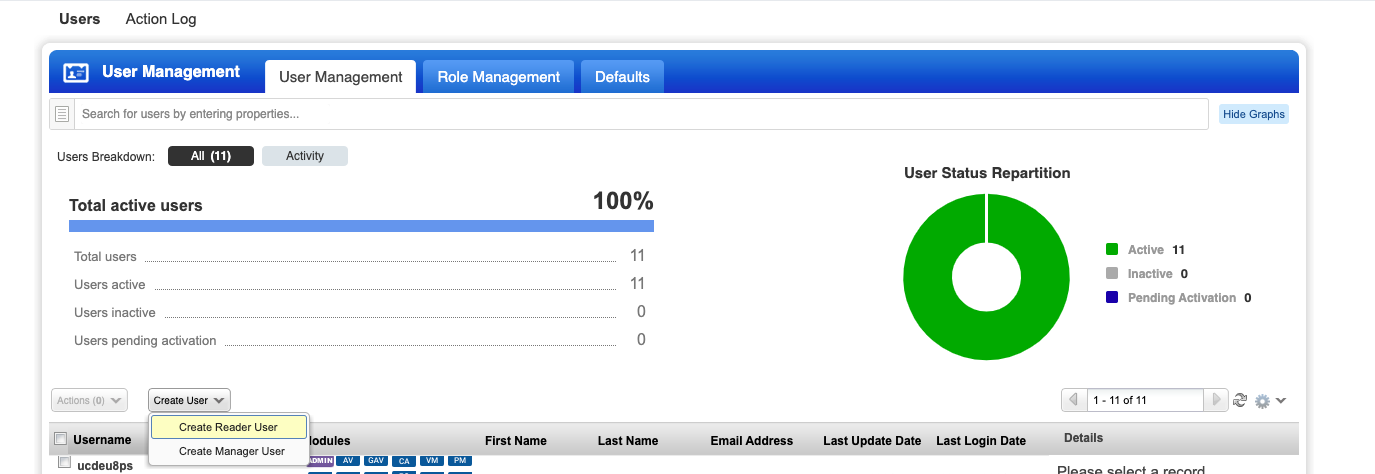
Select the user role as Reader (or a higher role) on the NewReaderUser page.
Mark the API and GUI access checkboxes.
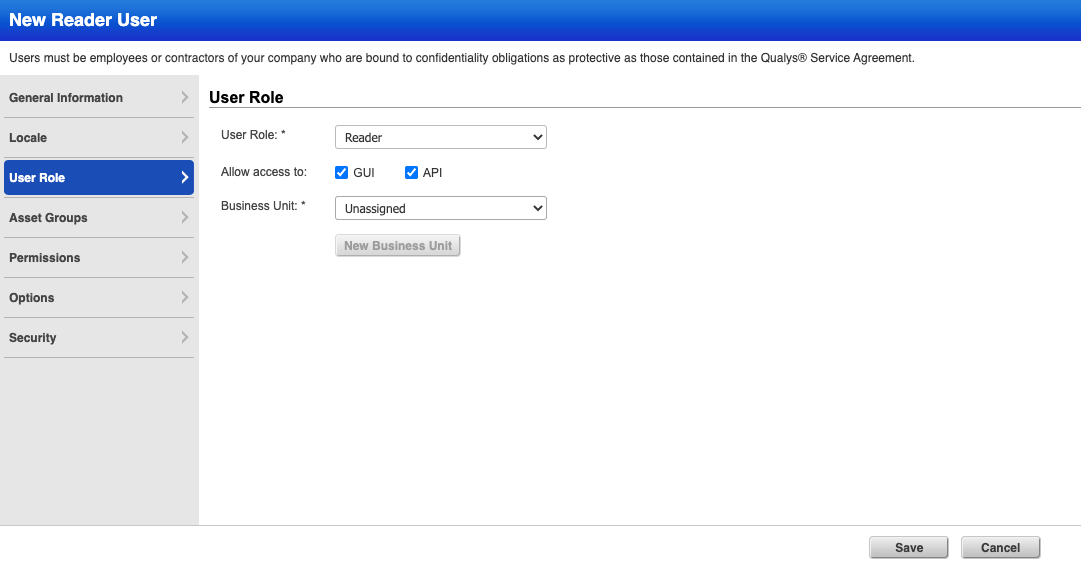
Click Save. The new user will get an email to verify login and complete the user registration process. We can now use the credentials to connect SAFE with Qualys.
Notes
Following step 6, UI access as configured in step 5 can be removed if required as the API user does not require UI access following setup. UI access may be required to perform certain troubleshooting steps.
Configure Qualys SCA and PC
To configure Qualys SCA in SAFE:
Log in to your SAFE account as Admin.
Click on the Integrations, from the left navigation.

Click the Qualys SCA card.
Enter the Qualys API URL, Username, and Password.
Enter the Policy IDs Filter. SAFE allows you to filter the assessment data being fetched from Qualys based on Qualys Policy IDs. If this field is blank, the system pulls the assessment data for all policies to which the user has access.
Enter the Auto-Sync Frequency.
Select the AutoOnbaordNewAssets checkbox to onboard the newly discovered assets in SAFE.
Click the Test Connection button.
Once the connection is verified, click Save Configuration.
Click the Sync Now button to fetch the results in SAFE.
.png)
View Result
After a successful sync, the Qualys SCA assets are automatically imported into SAFE.
View Assets
Go to the integration homepage.
Scroll to find the Qualys SCA integration card or search for Qualys SCA in the search bar.
Click on the Qualys SCA integration card for Finding View and Asset View.
Finding View: This tab displays all the findings details pulled from Qualys SCA.

Asset View: This tab displays all the Asset details pulled from Qualys SCA.

FAQ
1. I am receiving a “ Test Connection failed with Error: Unauthorized : Qualys Server Request failed with status code 401” Error, what should I do?
Normally 401 error means that your user is not authorised to access Qualys.
A helpful sanity check is to access the Qualys UI and log in with the username and password you have configured for the API user to confirm that access is working and that you can see the assets you expect.
If you cannot access the Qualys application, you should review the username/password settings.
API users cannot use SSO. If you have configured Qualys to use SSO for all users, you will need to disable SSO for the API user. To do so follow this Qualys documentation, Go to Users > Users and edit the user's account. You'll see the SAML SSO option in the Security section. Once SSO is disabled, check that you can access the Qualys UI.