About this document
This document gives step-by-step instructions on how to upload NIST CSF Assessment data in SAFE.
Introduction
SAFE allows you to bring your NIST CSF Questionnaire assessment data in SAFE. The system ingests the assessment into SAFE's risk scenario scoring algorithm. By providing your latest NIST CSF assessment to SAFE, you'll receive Prioritized Actionable Insights and Breach Likelihood based on the information.
Info: The questionnaire requirements are based on NIST CSF v1.1.
Upload Instructions
SAFE allows you to download the NIST CSF Questionnaire template in either CSV or Excel Format.
Here is a step-by-step procedure for uploading the NIST CSF Questionnaires in SAFE:
Navigate to Groups.
Click on the Group if you want to assess the NIST CSF Questionnaire.
Click the Questionnaire tab and then click NIST CSF Questionnaire.
If the NIST CSF Questionnaire is not available for a group, it means that you did not include it during the group's creation. You can edit and add the NIST CSF Questionnaire to a group.Click the + Upload button.
Click the Download Template drop-down.
Click either CSV or Microsoft Excel template. The system automatically downloads the template to your computer.
The template is available in CSV and Microsoft Excel formats. Decide which format works best for you.Microsoft Excel Format: If you choose Excel, you'll find instructions on the first sheet and the questionnaire for assessment on subsequent sheets. The Excel format provides a quick drop-down in the options column, making it easy to select an answer.
CSV Format: If you choose CSV, you must manually write the answer in the CSV format.
Open the downloaded template in your chosen format.
Review the NIST requirement in the "Standard Clause" column and select the appropriate option in the "Option" column. There are six options available for each question. Refer to Tier Definition for more details.
Tier 1 - Partial
Tier 2 - Risk Informed
Tier 3 - Repeatable
Tier 4 - Adaptive
Not Applicable
Not Implemented
Save the assessment file in a CSV format. This ensures compatibility for uploading the data into SAFE.
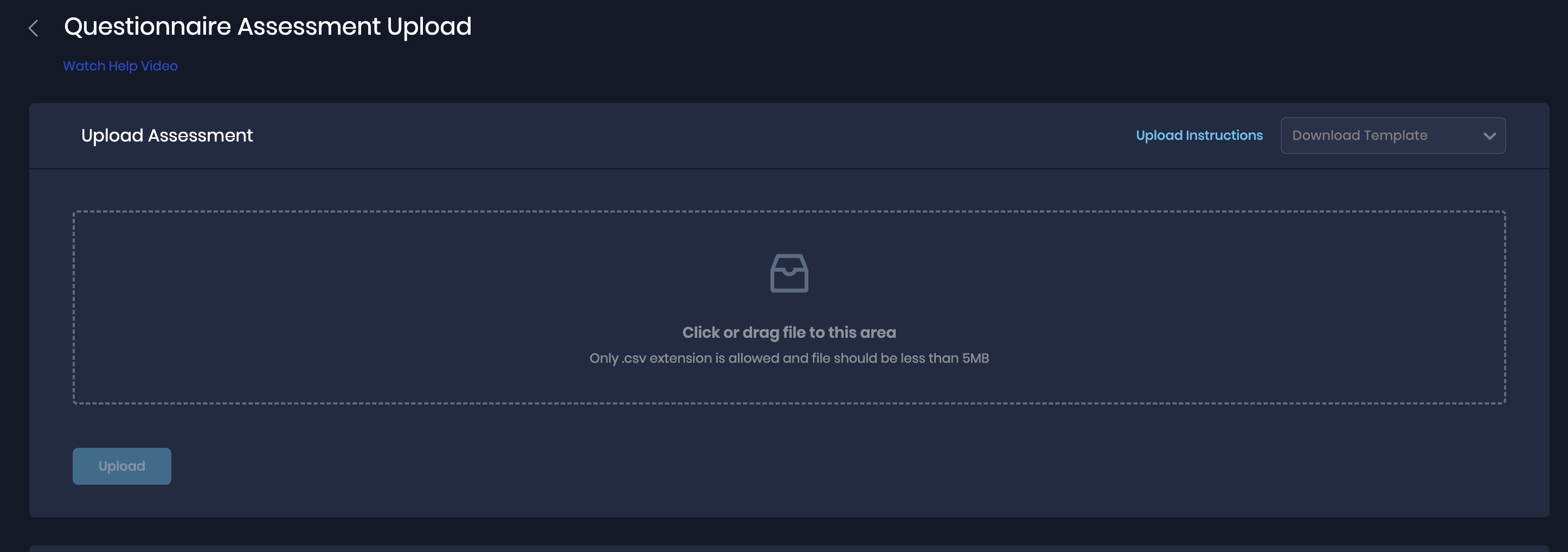
Go to the NIST CSF Assessment Upload page, and browse and upload the file. Alternatively, you can drag the file to the upload area on this page.
For a successful upload, the system displays a success message. You can see the upload details in the Upload History table available at the bottom of the page.
Microsoft Excel CSV Formats
Please ensure that you export the CSV using the "CSV (Command Delimited))(*.csv) option. Other file formats may result in errors.
Make sure that the chosen settings include commas as the delimiter. Refer to Microsoft documentation here.
Tier Definition for NIST CSF
Tier 1 | Partial | Risk management practices are not formalized, and risk is managed ad-hoc and sometimes reactive. Prioritization of cybersecurity activities may not be directly informed by organizational risk objectives, the threat environment, or business/mission requirements. |
Tier 2 | Risk-Informed | Risk management practices are approved by management but may not be established as organizational-wide policy. Prioritization of cybersecurity activities and protection needs is directly informed by organizational risk objectives, the threat environment, or business/mission requirements. |
Tire 3 | Repeatable | Risk management practices are formally approved and expressed as policy. Organizational cybersecurity practices are regularly updated based on the application of risk management processes to changes in business/mission requirements and a changing threat and technology landscape. |
Tire 4 | Adaptive | Risk management practices are based on previous and current risk management activities, including lessons learned and predictive indicators. Through a process of continuous improvement incorporating advanced cybersecurity technologies and practices, the organization actively adapts to a changing threat and technology landscape and responds in a timely and effective manner to evolving sophisticated threats. |
Not Applicable | Not applicable to the organization. | |
Not Implemented | Risk management practices are non-existent as controls have not been established. |